Your funds are your responsibility

Today, I want to address a crucial topic: the security of your crypto wallets.
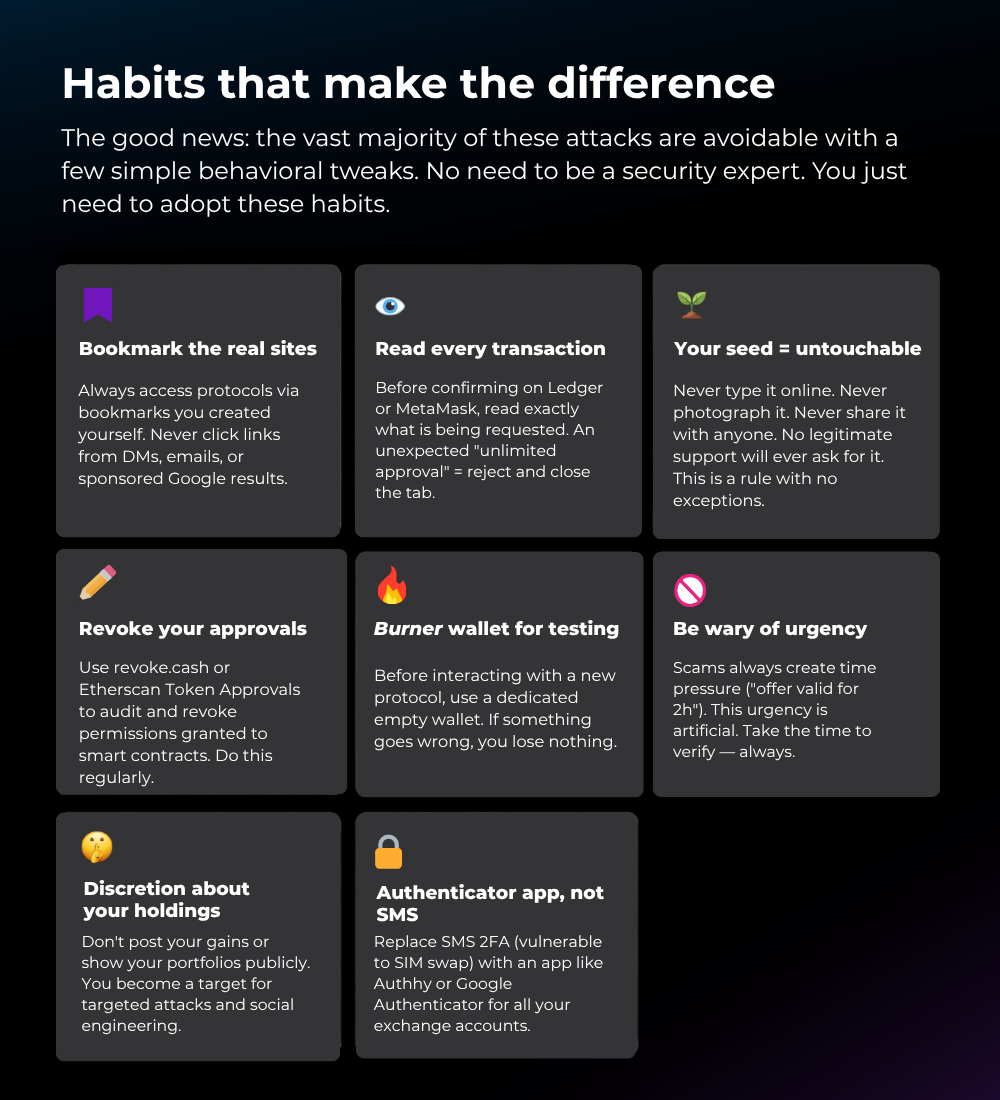
Even with reputable tools, protecting your funds relies primarily on your vigilance.
In crypto, there's no bank to call you, no customer service to cancel a transaction; a signature is all it takes.
One second of inattention is all it takes. This guide is what our community has learned the hard way.
Number of crypto thefts according to security experts:
- $3.8B stolen in 2022
- $1.7B stolen in 2023
- 95% of losses are preventable
All forms of crypto fraud
These four cases are just the tip of the iceberg. Here is a comprehensive overview, organized by threat type. Understanding each category means knowing where to look before you act.
Phishing & social engineering
- Fake sites (DeFi, CEX, bridges)
A near perfect replica of an official site. Slightly different URL (curve-fi(.)io instead of curve.fi). Goal: to capture your credentials or get you to sign a malicious transaction. - Fake airdrops / NFT mints
Mass distribution of unsafe links. The page requests a wallet connection and triggers a 'setApprovalForAll' transaction that hands over control of all your assets. - Malicious Google Ads links
Hackers buy ads on the names of popular protocols. The first Google result can lead directly to a fake site. Never click on sponsored results. - Fake wallets & browser extensions
Apps imitating MetaMask, Phantom, or Trust Wallet available on unofficial stores. They transmit your seed phrase to attackers upon import. - Phishing emails
Fake exchange emails (Binance, Coinbase) reporting "suspicious activity" or requesting an "urgent KYC verification". The link redirects to a fraudulent site.
Social engineering & impersonation
- Fake support (Discord, Telegram, X)
Immediate DMs after requesting support → seed theft or account takeover. - Fake influencers
Copied accounts offering "private alpha" or guaranteed investments. - Romance scams / pig butchering
Relationship built up → redirect to fake platform → total loss. - Fake crypto recruiters
Test using personal funds or a trojanized application → malware. - Deepfakes & AI calls
Use of AI to imitate the voice or face of a project leader or someone close to you during a call. Goal: create urgency and obtain a transfer or seed phrase.
Malware & technical attacks
- Clipboard hijacker
Malware that monitors your clipboard. When you copy a crypto address, it silently replaces it with the hacker's address. You send your funds without realizing it. - Keyloggers & info stealers
Capture everything you type: seed phrases, passwords, 2FA codes. Often hidden in pirated software, "cracked tools," or malicious PDF/Excel files. - Malicious browser extensions
Some Chrome extensions request overly broad permissions and can read your page data, intercept your private keys, or modify transactions on the fly. - SIM swapping
The attacker convinces your phone carrier to transfer your number to their SIM. They intercept your 2FA SMS messages and access your exchange accounts. Switch to an authenticator app. - BGP / DNS attacks
Advanced level: the attacker redirects network traffic from a legitimate protocol to their server. The URL is correct, the SSL certificate is valid, but the site is under hostile control.
Investment scams
- Rug pulls
A project team leaves with the liquidity → token = 0. - Pump & dump
Organized group that buys a low-liquidity tokens, while creating hype on social media... - Fake trading/investment platforms
Unrealistic returns → withdrawals blocked. - Giveaway scams
"Send 1 ETH, receive 2" → always fake. - Honeypot tokens
They can be bought, but not sold.
On-chain attacks & malicious contracts
- Token drainers via approval
One signature = unlimited access to your funds. - "Poison" NFTs and tokens sent to your wallet
NFTs appear in your wallet without any action on your part. When you try interact or sell them, a malicious function in the contract will be executed – often a drainer. - MEV/sandwich attacks
Bots exploit your slippage → instant loss. - Flash loans & exploits
Exploitation of vulnerabilities in smart contracts to drain liquidity pools. Less of a direct risk for users than for the protocols themselves, but your deposited funds are affected.
Useful tools
- Check if your email has been compromised: https://haveibeenpwned.com
- Find out how long it would take (seconds, minutes, hours, days, years, or even centuries) to crack a password based on its complexity: https://time2crack.eu
A single read can prevent an irreversible loss. In crypto, there is no going back. The security of your assets depends entirely on your own discipline.
With love and respect,
Y